ISO 27001:2022 is an international information security management standard. The ISO/IEC 27001 standard provides companies of all sizes across industries with guidance for establishing, implementing, maintaining and continually improving an information security management system. Compliance with ISO 27001:2022 means an organization is implementing a systematic approach to data security, managing risks, and safeguarding sensitive information to ensure its confidentiality, integrity, and availability. This standard is like a 'Gold Standard’ for keeping information safe. It defines varied controls and requirements to help organizations identify and manage information security risks effectively, comply with legal and regulatory requirements, and protect against potential threats to information security.
In this article, readers will understand the following sections that are a part of ISO 27001:2022 Annexures comprising of information deletion, safe disposal of media, management of removable media, reusing IT equipment, and maintaining a clear desk & screen policy, all ensuring information security.
Role of ISO 27001:2022 in Information Security
Beyond its framework, ISO 27001:2022 sets multiple controls for information security management for various industries such as organizational, people, physical, and technological. The controls aim to protect sensitive information and mitigate the risk to the organization with respect to data availability, confidentiality & maintaining its integrity. The physical control, as listed in Annexure 7.10 and Annexure 7.14 emphasis on the data handling requirement along with secure data disposal of obsolete equipment. The technological controls of Annexure 8 give clear direction on information deletion when it is no longer needed, Disposal of Media, and Management of Removable Media. ISO standard further directs organization to use a utility program that overwrites the data and performs secure data erasure or appoint a vendor to handle IT asset disposition. ISO 27001-2022, therefore directs organizations toward a risk-aligned, structured approach, safeguarding informational assets and affirming commitment to data security and integrity.
Secure Disposal of Confidential Data by ISO 27001:2022
For the purpose of data protection and its secure disposal, ISO 27001:2022 provides detailed requirements within the Information Security Management System (ISMS). The scope of ISMS is set by top management and the ISMS steering committee. The standard mandates organizations to conduct information security risk assessments, deploy physical controls over storage media, and ensure secure data erasure for re-use of equipment. ISO 27001:2022 introduces 11 new technological controls in comparison to ISO 27001:2013 and updates existing ones to enhance data security through specific procedures and guidelines, ensuring data does not fall into the wrong hands. Further, these 11 controls are a part of Annexure A and are referred to as ISO 27002:2022 supplementing ISO 27001:2022 standard. It is worthy to note that ISO 27002:2022 is not a certification standard.
We will delve deeper into how the various clauses and annexures address secure data disposal and its related aspects
This control ensures that companies should ensure the secure deletion of unnecessary information from their data-bearing devices to avoid unauthorized access. For this, the supplementary ISO 27002:2022 offers detailed guidance, including selecting appropriate deletion methods like overwriting, or encrypted deletion (Cryptographic erase). Organizations must document data deletion or data destruction processes, specify requirements in vendor contracts, and establish internal policies to manage and delete data effectively. This includes ensuring that all forms of data, such as files, folders, cached information that are no longer needed, are wiped. Physical deletion methods like degaussing or resetting devices to factory settings should be used, and cloud providers must comply with data deletion requirements to secure offsite data.
|
|
Control Type
|
Information Security Properties
|
Cybersecurity Concepts
|
Operational Capabilities
|
Security Domains
|
|
Organizational
|
Confidentiality, Integrity
|
Data Lifecycle Management, Data Minimization, Data Protection
|
Automated Software based Deletion, Compliance, Vendor Management, Documentation
|
Data Security, Compliance, Risk Management
|
Protection
|
Annexure A.8.3.2: Disposal of Media
Control 8.3.2, found in Clause 8 of Annexure A in ISO 27001:2022, focuses on the "Disposal of Media." This control sets strict rules for safely getting rid of media (like hard drives, SSD or USB drives) that contain sensitive information. This control mandates methods such as data erasure using a utility software that overwrites data to wipe it permanently, shredding, or degaussing media (using magnets to erase data). These methods ensure that the data cannot be recovered by anyone. ISO mentions shredding and degaussing for data destruction. However, it also emphasizes that organizations should adopt a strategy to reuse devices if they are in good condition. In such cases, data erasure is a recommended solution over physical destruction methods.
Annexure A.8.3.1: Management of Removable Media
Control 8.3.1, in Clause 8 of Annexure A of ISO 27001:2022, focuses on the management of removable media such as USB drives and DVDs. This control requires organizations to implement procedures for using, storing, and disposing of removable media based on their classification scheme.
Key guidelines include making the contents of reusable media unrecoverable when no longer needed, requiring authorization and maintaining records for media removal to ensure an audit trail, and storing media securely per manufacturers' standards. Cryptographic techniques should protect sensitive data, and data should be transferred to fresh media before becoming unreadable. Important data should have multiple copies on different media to prevent loss. Registration of removable media and its use for business purposes only are essential, and disposable media should be monitored and supervised during data transitions to ensure proper control and approval.
Annexure A Control 7.14: Secure Disposal or Re-use of Equipment
Control 7.14 under Clause 7, Physical Controls, in Annexure A of ISO 27001:2022, titled "Secure Disposal or Re-use of Equipment," lays down a rigorous framework to ensure the secure disposal or re-use of IT Assets (equipment). The control mandates a verification process to ascertain the removal or secure overwriting of any sensitive data and licensed software prior to disposal or re-use. This verification process serves as a critical measure to prevent unauthorized access to sensitive data, thereby upholding the confidentiality and integrity of organizational information.
By adhering to Control 7.14, organizations exhibit a meticulous approach towards the secure handling of equipment, reinforcing a robust information security infrastructure and demonstrating a profound commitment to safeguarding valuable informational assets.
Annexure A Control 7.10: Ensuring Security of Storage Media
Control 7.10 under Clause 7, Physical Controls, in Annexure A of ISO 27001:2022, titled "Storage Media Control," underpins a rigorous management framework for storage media throughout their life cycle of acquisition, use, transportation, and disposal. This control mandates adherence to the organization’s classification scheme and handling requirements, thereby ensuring streamlined, compliant management of storage media.
Attributes of Control 7.10
| Control Type |
Information Security Properties |
Cybersecurity Concepts |
Operational Capabilities |
Security Domains |
|
Preventive
|
Confidentiality, Integrity, Availability
|
Protect
|
Physical Security, Asset Management
|
Protection
|
Annexure A Control 7.7: Clear Desk and Clear Screen Policy
Annexure A of ISO 27001:2022, in Clause 7, highlights Physical Controls crucial for ensuring the confidentiality, integrity, and availability of an organization's information assets. Specifically, Clause 7.7 titled "Clear Desk and Clear Screen Control" delineates a framework aimed at mitigating risks associated with unauthorized access, information damage, or loss while handling papers and removable storage media. The control statement necessitates the formulation and enforcement of clear desk and clear screen rules within information processing facilities. This obligation propels organizations to devise stringent policies, thereby bolstering the physical security of sensitive information too.
How BitRaser Data Erasure Software Helps Comply with ISO 27001:2022?
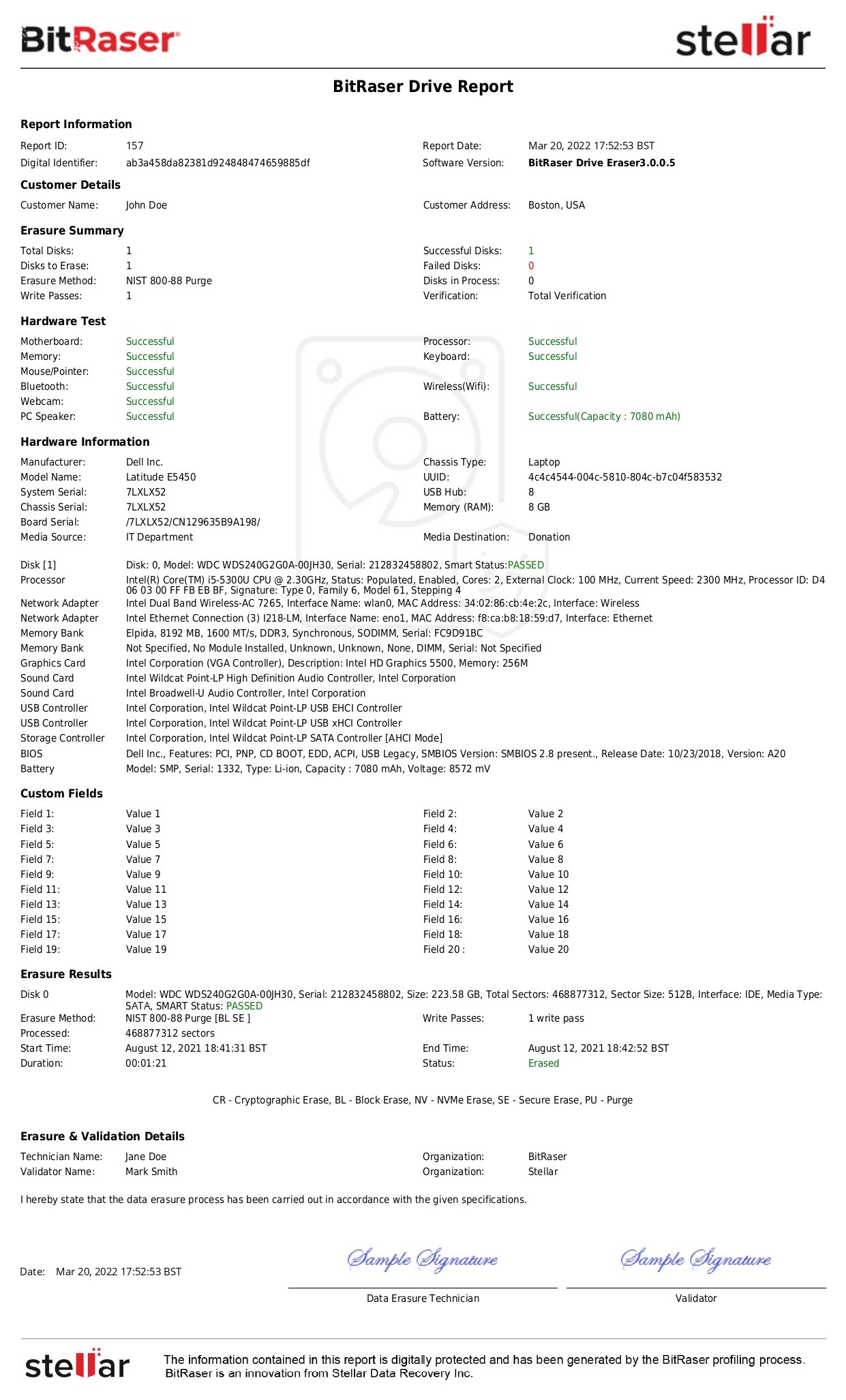
BitRaser helps organizations comply with ISO 27001:2022 standard by providing a certified software to perform secure and permanent data erasure during IT asset reallocation, disposal or return. The software securely wipes data from various drives and devices and leaves no recoverable traces. BitRaser software produces tamper-proof certificates of data destruction, which offer audit trails along with verifiable proof of data eraser. The software is tested and certified by global bodies like Common Criteria, ADISA, STQC, NYCE, Ontrack for its data erasure efficacy. These capabilities can assist organizations in meeting the rigorous requirements of ISO 27001:2022, especially the annexures that focus on secure data disposal. Therefore, organizations that prioritize data security and regulatory compliance find BitRaser an essential tool.
Conclusion
ISO 27001:2022 outlines guidelines for strong information security, focusing on data disposal, deletion, and media management. It provides a structured framework for securely handling sensitive data, ensuring protection and compliance. Key controls include secure data deletion, media disposal, and equipment reuse. Organizations must practice safe disposal for redundant or obsolete data and follow data erasure protocols for reusable devices. For non-functional devices, physical destruction is allowed.